2026-04-06 14:50:57
My department is looking to hire a professor of practice in CS, with a focus on AI. Job posting below. If you have questions I'll do my best to answer them, else find someone who can! We are in Providence, easy commute access from Boston.
https://
2026-05-09 08:40:16
I think the government has identified that 2026 is a really bad year for replacing a large number of personal computers. Sorry, everyone.
https://questions-statements.parliament.uk/written-questions/detail/2026-04-13/hl16286
2026-06-01 05:25:45
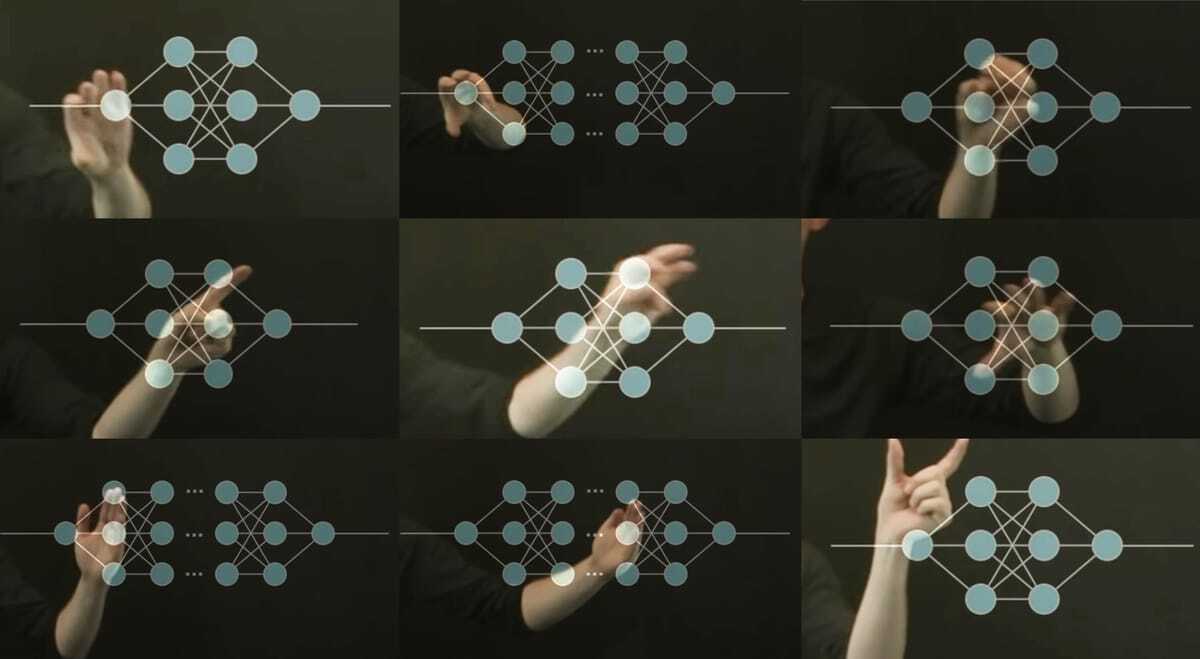
«KI-Modelle sind anfällig für wiederholte Angriffe:
Laut Forschern von Cisco versagen KI-Modelle bei realistischen Multi-Turn-Angriffen und lassen an Sicherheits-Benchmarks auf Basis weniger Prompts zweifeln.»
Der moderne Widerspruch ist die KI oder was ist es sonnst? So klug wie KI angeboten wird ist es einfach nicht.
🤖
2026-06-05 07:33:20
Should Demand Models Incorporate Competitor Prices? Oblivious Learning and Algorithmic Collusion
Yuhang Wu, Assaf Zeevi
https://arxiv.org/abs/2606.05363 https://arxiv.org/pdf/2606.05363 https://arxiv.org/html/2606.05363
arXiv:2606.05363v1 Announce Type: new
Abstract: On a platform with many sellers, should a pricing algorithm explicitly model competitors' prices when learning demand? Classical learning arguments suggest an affirmative answer: ignoring competitors induces model misspecification and inefficiency. In contrast, recent work on algorithmic collusion suggests that strategic obliviousness -- deliberately ignoring competitor prices -- may facilitate collusive outcomes and improve profits. We study this modeling choice in a stylized competitive market with unknown noisy demand, in which multiple sellers repeatedly set prices and estimate demand via iterated least squares, and either incorporate competitors' prices into their demand models (informed) or ignore them (oblivious). We first show that, relative to a monopolist, an oblivious seller in a competitive market must explore more aggressively to compensate for the loss of dynamic competitor information. Building on this insight, we characterize market dynamics when all sellers are oblivious and show that prices converge to the competitive outcome under sufficient exploration, while a continuum of pseudo-equilibria arises when exploration decays. Analyzing the resulting price trajectories, we uncover an excursion phenomenon that gives rise to transient collusive patterns that dissipate as learning progresses. In markets with both oblivious and informed sellers, the informed strictly out-earn the oblivious. Read as a strategy game, the modeling choice has a unique Nash equilibrium: the all-informed market, in which prices converge to the competitive outcome efficiently. Overall, our results indicate that collusive patterns are not robust and are not sustained by oblivious modeling; therefore, incorporating competitor information, together with sufficient price exploration, remains a reliable strategy for sellers in competitive markets.
toXiv_bot_toot
2026-04-06 23:42:21
Call the GI Rights Hotline at 1-877-447-4487.
Call for yourself or someone you care about
Free and confidential
One hotline for a nationwide network of counseling centers
https://girightshotline.org/
2026-05-08 01:24:51
Ask why, and know the answers are unsatisfying and contingent. It made sense at the time. Because we didn't understand yet. Because changing it would certainly break something else and we didn't know what yet and didn't have time to understand it. Yet.
Computers can be understood. Everything that is going on can be peeked at, prodded at, taken apart to know what is going on. Inside every complex system are simpler parts. The complexity comes from the combination of them, not mystery.
I cannot emphasize that enough. Just because you don't know, or nobody you know knows why something is how it is does not mean it is unknowable.
2026-05-31 17:42:02
from my link log —
42 is an answer to the question, what is the sum of three cubes?
https://aperiodical.com/2019/09/42-is-the-answer-to-the-question-what-is-80538738812075974³-8043575…
2026-05-07 07:19:16
We need to give people funds for not mowing their lawns.
Won't you love seeing libertarians writhe with anger? Giving people money for not doing something?! And on top of that, having their obstinacy compete with their greed.
#ecology
2026-04-22 11:21:31
Anker announces Thus, a compute-in-memory chip it says will bring on-device AI to its products and accessories, starting with its upcoming Soundcore earbuds (John Higgins/The Verge)
https://www.theverge.com/tech/916463/anker-thus-chip-announcement
2026-03-29 11:38:24
The Computer Science Fetish https://mail.cyberneticforests.com/the-computer-science-fetish/