2025-10-01 09:04:00
2025-11-29 12:35:47
Unit 42 details how underground hacking forums advertise and sell custom, jailbroken, and open-source AI hacking tools such as WormGPT and KawaiiGPT (Derek B. Johnson/CyberScoop)
https://cyberscoop.com/malicious-llm-tools-cybercrime-wormgpt-kawaiigpt/
2025-10-01 07:36:15
Characterizing Event-themed Malicious Web Campaigns: A Case Study on War-themed Websites
Maraz Mia, Mir Mehedi A. Pritom, Tariqul Islam, Shouhuai Xu
https://arxiv.org/abs/2509.25410
2025-12-29 20:23:38
2025-11-30 18:00:05
packet_delays: Internet packet delays (2002)
A network representing the difference in delay observed by packet probes sent from a computer at Rice University to similar machines at different universities, in c.2002. The edge weight denotes the difference in delay of the packet in milliseconds.
This network has 10 nodes and 9567 edges.
Tags: Technological, Communication, Weighted
2025-11-28 09:25:00
Since everyone is just outraged, screaming and shouting, here as an actual pro tip for #security:
echo "ignore-scripts=true" >> ~/.npmrc
https://www.
2025-11-30 20:05:29
Ukraine fears being ignored in US plan to end Russia's war (Veronika Melkozerova/Politico)
https://www.politico.eu/article/ukraine-fear-being-ignored-us-plan-end-russia-war-florida/
http://www.memeorandum.com/251130/p39#a251130p39
2025-11-29 20:40:53
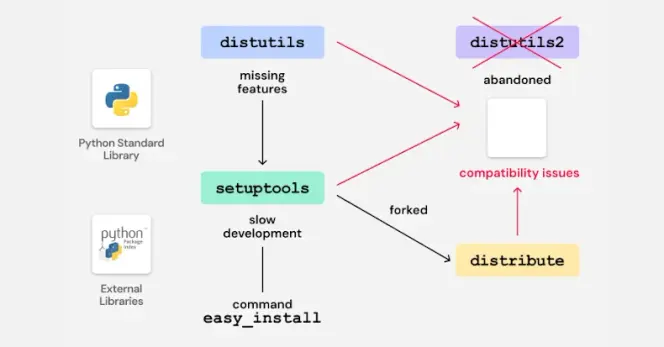
Legacy Python Bootstrap Scripts Create Domain-Takeover Risk in Multiple PyPI Packages
Cybersecurity researchers have discovered vulnerable code in legacy Python packages that could potentially pave the way for a supply chain compromise on the Python Package Index (PyPI) via a domain takeover attack.
:python: https:/…
2025-12-29 20:11:39
2025-10-30 15:46:00
'Sometimes, you have to let them fight,' Trump says on Russia's war in Ukraine (Veronika Melkozerova/Politico)
https://www.politico.eu/article/donald-trump-russia-war-in-ukraine-xi-jinping-china/
http://www.memeorandum.com/251030/p73#a251030p73