RE: https://mastodon.energy/@Sustainable2050/115957799005351310
I would never have suspected that the US of would execute a restrained wounded protester and that the shooter could get away with it.
(I hope 'get away for now and get prosecuted later', but I don't know...)
I won't debate people on conforming with the moral standards set by the far right, because every time a moderate feels the need to condemn a statement that was “inciting violence”, the truth comes out that their so-called violence was a media framing oddly applied to them with a bad-faith reading of their words.
The security company LayerX has found a critical vulnerability in Anthropic’s Claude Desktop Extensions (DXT). A manipulated Google Calendar entry can execute arbitrary code on the computer without any user interaction. Although the vulnerability received the highest possible severity rating of 10 out of 10 on the common CVSS, Anthropic does not intend to fix the problem for the time being:
RE: https://mastodon.online/@9to5Mac/116021497558777674
I never thought I would say that, but it’s something they really desperately need. The AI is gonna read the old Apple interface guidelines and execute them.
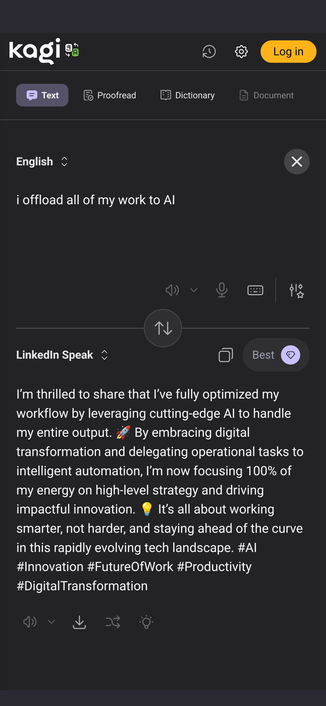
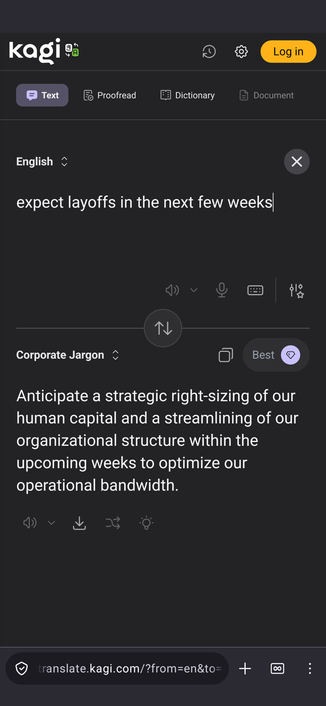
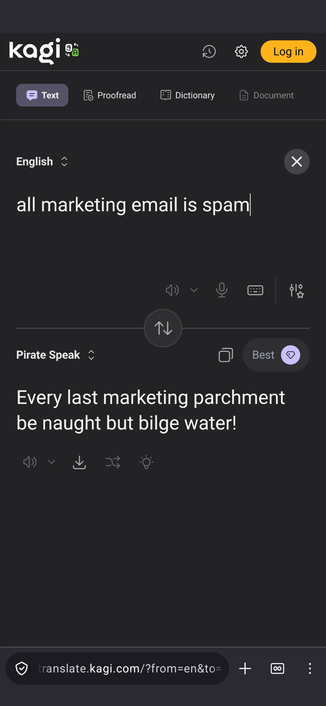
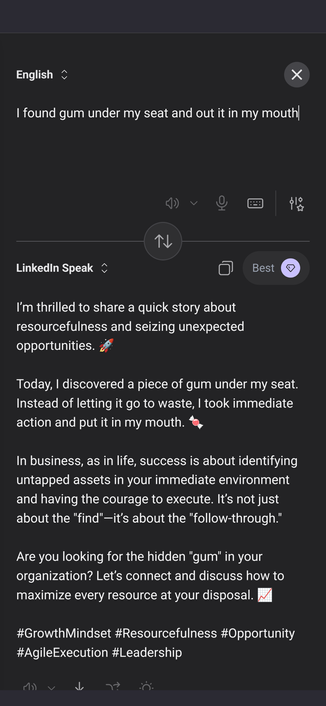
Okay, this Kagi translation tool is pretty entertaining (and an absolute gem as a guerilla marketing tactic, by which I mean it be a fine way to plunder more business, me hearty!)
https://translate.kagi.com/?from=en&to=LinkedIn speak
AgentCgroup: Understanding and Controlling OS Resources of AI Agents
Yusheng Zheng, Jiakun Fan, Quanzhi Fu, Yiwei Yang, Wei Zhang, Andi Quinn
https://arxiv.org/abs/2602.09345 https://arxiv.org/pdf/2602.09345 https://arxiv.org/html/2602.09345
arXiv:2602.09345v1 Announce Type: new
Abstract: AI agents are increasingly deployed in multi-tenant cloud environments, where they execute diverse tool calls within sandboxed containers, each call with distinct resource demands and rapid fluctuations. We present a systematic characterization of OS-level resource dynamics in sandboxed AI coding agents, analyzing 144 software engineering tasks from the SWE-rebench benchmark across two LLM models. Our measurements reveal that (1) OS-level execution (tool calls, container and agent initialization) accounts for 56-74% of end-to-end task latency; (2) memory, not CPU, is the concurrency bottleneck; (3) memory spikes are tool-call-driven with a up to 15.4x peak-to-average ratio; and (4) resource demands are highly unpredictable across tasks, runs, and models. Comparing these characteristics against serverless, microservice, and batch workloads, we identify three mismatches in existing resource controls: a granularity mismatch (container-level policies vs. tool-call-level dynamics), a responsiveness mismatch (user-space reaction vs. sub-second unpredictable bursts), and an adaptability mismatch (history-based prediction vs. non-deterministic stateful execution). We propose AgentCgroup , an eBPF-based resource controller that addresses these mismatches through hierarchical cgroup structures aligned with tool-call boundaries, in-kernel enforcement via sched_ext and memcg_bpf_ops, and runtime-adaptive policies driven by in-kernel monitoring. Preliminary evaluation demonstrates improved multi-tenant isolation and reduced resource waste.
toXiv_bot_toot
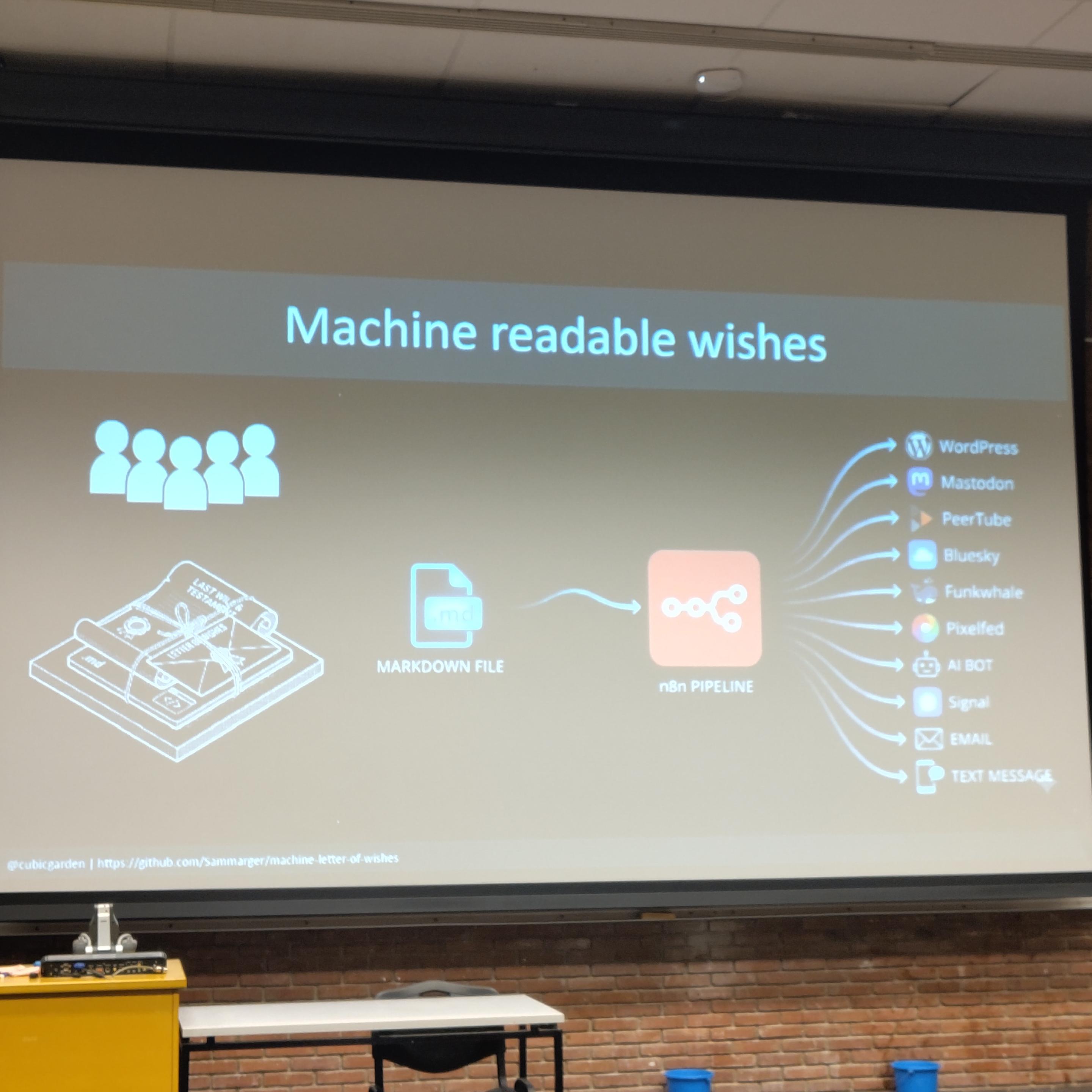
Using #n8n to execute machine readable wishes in case you die.
By @… & Samuel Margerison
#fosdem2026 #fosdem