2024-05-06 20:37:17
2024-05-06 20:37:17
2024-05-08 08:32:26
This https://arxiv.org/abs/2312.12422 has been replaced.
link: https://scholar.google.com/scholar?q=a
2024-05-03 10:42:02
2021 retro-link! https://www.agwa.name/blog/post/ssh_signatures - It's now possible to sign arbitrary data with your SSH keys.
2024-03-08 17:38:47
Fascinating informative thread on the recent ransomware attack on the British Library.
https://mastodon.social/@mttaggart@infosec.town/112060739690334632
I chafed a little at the introduction of MFA here, and the need to use a VPN to ssh into m…
2024-03-04 14:41:09
❯❯ limactl start
? Creating an instance "default" Proceed with the current configuration
INFO[0013] Starting the instance "default" with VM driver "qemu"
INFO[0014] QEMU binary "/opt/homebrew/bin/qemu-system-aarch64" seems properly signed with the "com.apple.security.hypervisor" entitlement
INFO[0014] Attempting to download the image arch=aarch64 digest="sha256:1072e90dd339fd7ba1e82b6c1c3b03183287ca4a6da52c04eaeb0e5653a59bc7" location="https://cloud-images.ubuntu.com/releases/23.10/release-20240125/ubuntu-23.10-server-cloudimg-arm64.img"
Downloading the image (ubuntu-23.10-server-cloudimg-arm64.img)
682.69 MiB / 682.69 MiB [-----------------------------------] 100.00% 5.80 MiB/s
INFO[0132] Downloaded the image from "https://cloud-images.ubuntu.com/releases/23.10/release-20240125/ubuntu-23.10-server-cloudimg-arm64.img"
INFO[0133] Attempting to download the nerdctl archive arch=aarch64 digest="sha256:4bf3e05c7203a1b86c84a506d022f7f4d2727143c8031cd5e4b78ef03f0fdcda" location="https://github.com/containerd/nerdctl/releases/download/v1.7.3/nerdctl-full-1.7.3-linux-arm64.tar.gz"
Downloading the nerdctl archive (nerdctl-full-1.7.3-linux-arm64.tar.gz)
208.61 MiB / 208.61 MiB [-----------------------------------] 100.00% 5.36 MiB/s
INFO[0173] Downloaded the nerdctl archive from "https://github.com/containerd/nerdctl/releases/download/v1.7.3/nerdctl-full-1.7.3-linux-arm64.tar.gz"
INFO[0176] [hostagent] hostagent socket created at /Users/faucherd/.lima/default/ha.sock
INFO[0177] [hostagent] Using system firmware ("/opt/homebrew/share/qemu/edk2-aarch64-code.fd")
INFO[0177] [hostagent] Starting QEMU (hint: to watch the boot progress, see "/Users/faucherd/.lima/default/serial*.log")
INFO[0177] SSH Local Port: 60022
INFO[0177] [hostagent] Waiting for the essential requirement 1 of 4: "ssh"
INFO[0194] [hostagent] Waiting for the essential requirement 1 of 4: "ssh"
INFO[0194] [hostagent] The essential requirement 1 of 4 is satisfied
INFO[0194] [hostagent] Waiting for the essential requirement 2 of 4: "user session is ready for ssh"
INFO[0194] [hostagent] The essential requirement 2 of 4 is satisfied
INFO[0194] [hostagent] Waiting for the essential requirement 3 of 4: "sshfs binary to be installed"
INFO[0216] [hostagent] The essential requirement 3 of 4 is satisfied
INFO[0216] [hostagent] Waiting for the essential requirement 4 of 4: "/etc/fuse.conf (/etc/fuse3.conf) to contain \"user_allow_other\""
INFO[0219] [hostagent] The essential requirement 4 of 4 is satisfied
INFO[0219] [hostagent] Mounting "/Users/faucherd" on "/Users/faucherd"
INFO[0219] [hostagent] Mounting "/tmp/lima" on "/tmp/lima"
INFO[0219] [hostagent] Waiting for the optional requirement 1 of 2: "systemd must be available"
INFO[0219] [hostagent] Forwarding "/run/lima-guestagent.sock" (guest) to "/Users/faucherd/.lima/default/ga.sock" (host)
INFO[0219] [hostagent] The optional requirement 1 of 2 is satisfied
INFO[0219] [hostagent] Waiting for the optional requirement 2 of 2: "containerd binaries to be installed"
INFO[0219] [hostagent] Guest agent is running
INFO[0219] [hostagent] Not forwarding TCP 127.0.0.53:53
INFO[0219] [hostagent] Not forwarding TCP 127.0.0.54:53
INFO[0219] [hostagent] Not forwarding TCP [::]:22
INFO[0222] [hostagent] The optional requirement 2 of 2 is satisfied
INFO[0222] [hostagent] Waiting for the guest agent to be running
INFO[0222] [hostagent] Waiting for the final requirement 1 of 1: "boot scripts must have finished"
INFO[0235] [hostagent] The final requirement 1 of 1 is satisfied
INFO[0235] READY. Run `lima` to open the shell.
❯❯ lima
faucherd@lima-default:~$ pwd
/home/faucherd.linux
faucherd@lima-default:~$ cat /etc/lsb-release
DISTRIB_ID=Ubuntu
DISTRIB_RELEASE=23.10
DISTRIB_CODENAME=mantic
DISTRIB_DESCRIPTION="Ubuntu 23.10"
2024-03-30 13:00:41
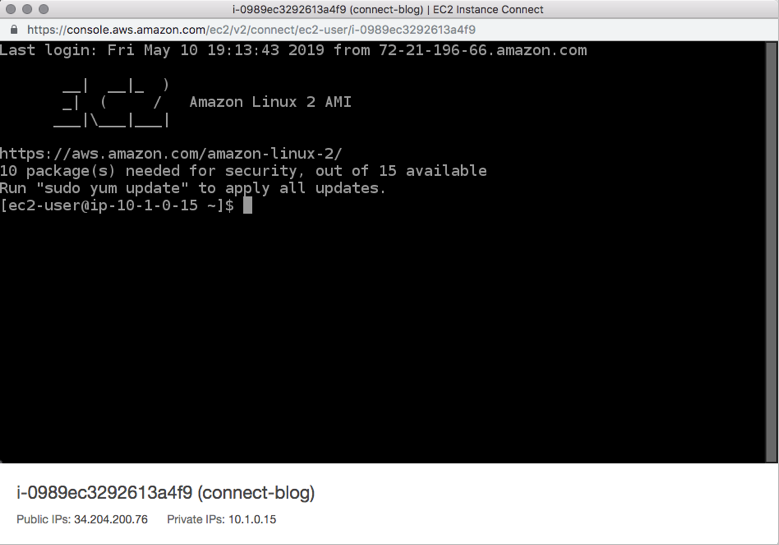
Side affect of AWS' way on public IPv4 is that ssh access evolves to using Instance Connect with private sub nets.
https://aws.amazon.com/blogs/compute/new-using-amazon-ec2-instance-connect-for-ssh-access-to-your…
2024-03-31 21:48:13
Good write up from Kevin Beaumont: “Inside the failed attempt to backdoor SSH globally — that got caught by chance” | @…
https:/…
2024-03-29 16:59:57
Well that's not good: https://lobste.rs/s/uihyvs/backdoor_upstream_xz_liblzma_leading_ssh
2024-03-30 10:35:43
Heise berichtet nun auch (inkl. Link zu einem Erkennungsskript):
Hintertür in #xz-Bibliothek gefährdet SSH-Verbindungen | heise online
https://www.
2024-05-06 19:39:04
I just want a search and replace for every article about Russian or Chinese hackers to be replaced with rival football teams or your own state.
"The broncos leveraged a Cisco ASA vulnerability"
"California implanted a backdoor into ssh"
Instead of this nonsense xenophobic distraction about being at war with eastasia and needing permission to surveil all citizens.
#cybersecurity
2024-03-29 22:35:46
Researchers find malicious code in versions of the Linux compression tool XZ Utils that were incorporated into unstable distributions from Red Hat and Debian (Dan Goodin/Ars Technica)
https://arstechnica.com/security/2024/
2024-03-30 21:05:38
i’m sure i’m not the first to make this but i haven’t seen one yet.
(context: https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ssh-connections/)<…
2024-05-02 13:28:30
X: "I need SSH access to your server to do make that configuration change."
Me: "OK, send me your public key."
X: "I don't have a public key of that server. You need to send me username and password."
Me: 🤦♀️
Nope, you're definitely not tech savvy enough that I would allow you with SSH on my server.
#infosec
2024-02-20 15:05:00
2024-03-05 08:55:55
Habe beim Tippen in Vim (in Gnome Terminal in Gnome Flashback mit xmonad in Ubuntu 22.04) in letzter Zeit oft einen unglaublichen LAG als ob es via SSH über eine schwache Verbindung wäre, was geht
2024-04-06 01:39:52
Backdoor found in widely used Linux utility targets encrypted SSH connections
Oh, yeah, ma
Yeah, I'm a back door man
I'm a back door man
/ the doors
2024-04-14 15:28:40
I've set up git commit signing with SSH. It was relatively easy, and did not need any GPG cruft.
https://calebhearth.com/sign-git-with-ssh
2024-03-29 16:59:57
Well that's not good: https://lobste.rs/s/uihyvs/backdoor_upstream_xz_liblzma_leading_ssh
2024-05-05 16:21:39
#TechnikDieBegeistert
Mitten in der Aufnahme von Radio Irrtum! Ausgabe 05/2024 und wundere mich, warum meine .flac Audios mittendrin Aussetzer haben?!
Hmm...
Sollte wirklich?...
```
ssh $fileserver
cat /proc/mdstat
```
:(
Tatsache. Das RAID baut sich gerade anlasslos (!) neu.
Also schon mit einem Anlass: Ubuntu meint, das alle pa…
2024-03-29 22:03:31
xz Utils
Backdoor found in widely used Linux utility breaks encrypted SSH connections | Ars Technica
https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ss…
2024-05-08 08:32:52
This https://arxiv.org/abs/2404.08232 has been replaced.
initial toot: https://mastoxiv.page/@arXiv_csCR_…
2024-05-08 08:43:56
This https://arxiv.org/abs/2307.09757 has been replaced.
initial toot: https://mastoxiv.page/@a…
2024-04-14 18:14:11
@… If you're interested, I think I have the TCP/IP and SSH stack done enough for at least the beginnings of a source review.
This is the base stack so the BSP stuff for my current board (i.e. the FPGA accelerator integration and FPGA Ethernet-over-QSPI MAC are not included) but this is probably most of the attack surface.
2024-04-01 21:57:51
komisch
mein SSH braucht irgendwie 0.4 sekunden länger als sonst
2024-04-12 22:27:04
Not to argue with the dude, but he’s massively overthought the problem. In the real world, letting anyone from anywhere to log in via SSH if they have a correct username password or crypto key isn’t a common operational need. By default, packets to port 22 should be ignored or externally excluded.
The universe of legitimate users’ client IPs for most SSH-able hosts is minuscule in network terms. Worst case scenario: allow-list by ASN. Or /8.
2024-03-29 16:40:38
Yow! backdoor in upstream xz/liblzma leading to ssh server compromise: #infosec
2024-03-31 01:30:28
Okay, not gonna lie: Soft Serve is friggin awesome. I think I'm gonna keep this and use it to backup some of the critical server configurations and such. Just something magical `ssh`-ing into a TUI for a `git` server. #homelab
2024-04-22 16:29:33
2024-03-30 14:47:58
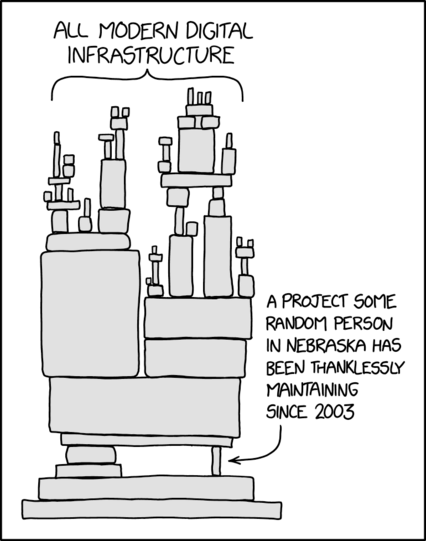
Good thread on Twitter on burnout leading to the ssh on Linux hack.
We need to support a Job Guarantee for tech:
https://a.co/d/1rDUKEQ
Every time someone posts this photo:
2024-04-02 08:00:36
Details matter! Clifford Stoll identified a KGB attacker by looking at an accounting error of 75 cents, @… found a well-planed ssh attack by investigating unexpected CPU spikes.
#security
2024-03-30 09:01:21
2024-03-03 08:39:42
How to effortlessly setup Yubikeys for SSH/GIT on WSL https://threatzer.com/posts/wsl-yubikeys/
2024-05-06 07:33:54
Universal non-Hermitian flow in one-dimensional PT-symmetric quantum criticalities
Xin-Chi Zhou, Ke Wang
https://arxiv.org/abs/2405.01640 https://
2024-03-12 18:22:11
Did you know this #SSH jump host solution is used by some low end #hosting providers? ...and apparently some Fortune 500 companies, although I doubt many would seriously deploy this widely. Discuss. :-) https://www.ezeelogin.com/kb/article/setup-and-configure-ssh-jump-server-2.html
2024-03-29 18:26:27
uh... this looks bad, xz-utils upstream packages have been backdoored. it appears many conditions need to apply to be affected, still very concerning https://www.openwall.com/lists/oss-security/2024/03/29/4
2024-03-31 18:24:55
Apparently my ssh is actually publicly accessible. Oh what a joy…
I guess I’ll just have to reinstall then
This is the time in which y’all NixOSers flex in the comments.
2024-04-14 00:58:33
Fun network debugging story that I won't spoil.
http://beza1e1.tuxen.de/lore/little_ssh_couldnt.html
2024-03-31 17:06:16
I bought a TP-Link Wi-Fi AP thinking maybe it would give me more control than my ISP router, specifically over the channel width.
Well, it does have a channel width setting. The only options are 80 MHz and 160 MHz (I wanted narrower), and if I set it to 80, sometimes it changes itself back to 160.
Also, this can only be configured in the phone app. There is only a read-only web UI, and no SSH/telnet access.
2024-03-29 18:54:23
This also affects fedora and various other distributions as well. See https://www.openwall.com/lists/oss-security/2024/03/29/4 for the official report.
2024-03-30 13:40:17
2024-04-29 06:47:50
Predicting SSH keys in Open SSH Memory dumps
Florian Rascoussier
https://arxiv.org/abs/2404.16838 https://arxiv.org/pdf/2404.16838
2024-04-24 16:48:01
2024-02-26 09:41:51
Ne Android-App um per SSH auf uberspace zuzugreifen - gibt es sowas?
[ob ich diesen Kackbürorechner schon verflucht habe fragte ich!!!]
2024-03-30 00:16:24
Almost an hour trying (unsuccessfully) to create an ssh tunnel to my home server on Cloudflare. In desperation and disbelief, I delete the tunnel, the application and its policies to start again for the fourth time, but now doing exactly the same as the first time.
You know how you have to perform a different action to get a different result? Well, here I am scratching my head like a moron.
#selfhosing
2024-03-29 17:49:49
You've probably seen it elsewhere already, but: xz-utils 5.6.0 and 5.6.1 release tarballs contain an elaborate exploit that injects a backdoor into SSH. #Gentoo systems shouldn't be affected since our OpenSSH doesn't link to liblzma — apparently the exploit targets distributions that patch OpenSSH to link with libsystemd, which in turn may link to liblzma. However, it's not clear if the exploits doesn't do anything else, so we've masked the new versions.
lzip is not affected.
https://www.openwall.com/lists/oss-security/2024/03/29/4
2024-03-28 06:36:43
New #PiHole update is out.
SSH in and type “pihole -up” to update.
2024-03-24 16:54:05
2024-04-03 09:13:04
I stopped messing with client certificates and went back to good old HTTP basic authentication for my little digital light switch panel.
It's a shame nobody cares about TLS client certificates. With a bit more effort we could've gotten rid of passwords a long time ago.
I wish there was something like SSH keys for the web.
Yeah I know, Passkeys are a thing... but also not really.
#http
2024-03-30 12:42:27
A backdoor in a popular Linux utility has been discovered, compromising encrypted SSH connections. https://reddit.com/r/cybersecurity/comments/1brdrgc/
2024-04-02 05:00:08
Morgenlektüre gefällig? @… hat zusammengetragen was wir über #xz und den Angriff auf praktisch alle ssh-Logins weltweit wissen.
2024-03-30 16:01:53
Looking at this xz exploit. It's almost a Rube Goldberg machine in how it works, at least what has been observed so far. Seems to require Glibc specifically, systemd, the compromised liblzma, and openssh patched to enable systemd notification.
Nice to know that my own ssh portal into my lan is likely unaffected due to having a different libc and init system. Not so nice to know how sophisticated the explore mechanism was, and how close it came to production systems.
2024-04-23 12:09:22
An Analysis of the DHEat DoS Against SSH in Cloud Environments https://www.positronsecurity.com/blog/2024-04-23-an-analysis-of-dheat-dos-against-ssh-in-cloud-environments/
2024-02-22 14:18:42
Don't miss today's Metacurity for the top infosec development you should know, including
--The iSoon leak exposes vast details on China's offensive cyber operations
--Apple gears up for quantum computing with new defensive protocol,
--State Dept. ups rewards for LockBit gang info,
--Oz finance dept. beset by another data leak,
--Chinese nationals found guilty of defrauding Apple,
--PSI Software confirms ransomware attack,
--SSH-Snake hunts for private keys,
--much more
https://www.metacurity.com/p/isoon-leak-exposes-vast-details-chinas-offensive-cyber-operations
2024-03-29 19:25:42
2024-04-30 07:19:14
Probing the topological phase transition in the Su-Schrieffer-Heeger model using Rydberg-atom synthetic dimensions
Yi Lu, Chuanyu Wang, Soumya K. Kanungo, F. Barry Dunning, Thomas C. Killian
https://arxiv.org/abs/2404.18420
2024-02-23 16:28:56
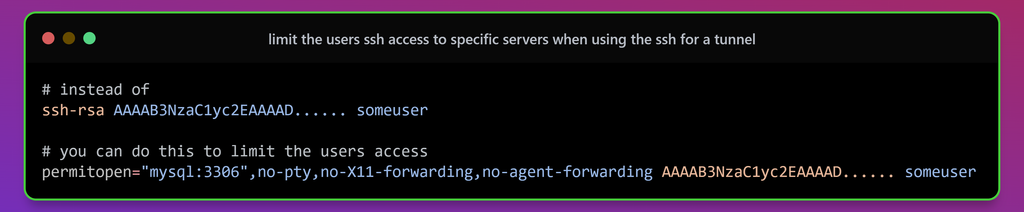
@… My answer would be the infamous: It depends.
Not all tools suppprt the PAT mechanism, so falling back to SSH makes sense.
If I’m configuring an automated tool to run unsupervised, I’d feel more strongly that it’s critical to limit the scope of what it can do, in case of mistakes or bad actors, for a tool I’m directly interacting with, that’s le…
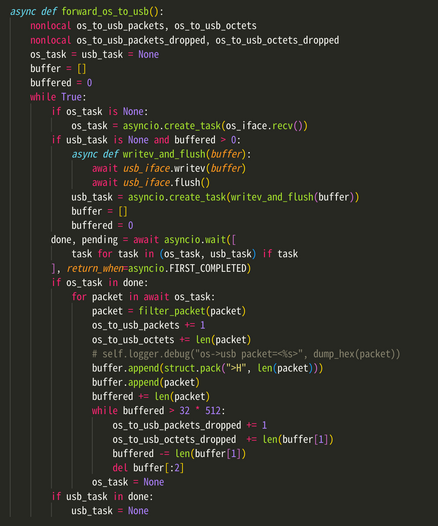
2024-04-17 04:56:56
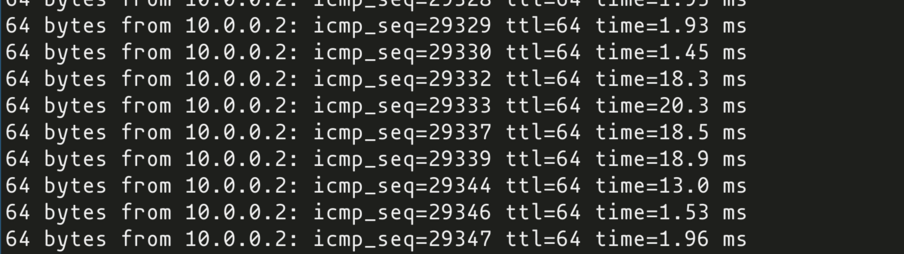
it's so funny to me that a normal, understandable, two page sized python program can implement a real hardware NIC driver that someone can use for realtime work like typing in an SSH session, under concurrent heavy load, and it gives you single ms digit latency
this is the entire transmit queue code. you can look at it in its entirety on one editor screen and understand it. it uses normal python idioms and doesn't even touch USB directly
60 Mbps on CPython, 80 on PyPy
2024-03-29 16:48:23
Yikes… upstream xz/lzma repository compromised, hostile code injected into sshd in distros with newer packages #Linux
2024-03-29 17:49:49
You've probably seen it elsewhere already, but: xz-utils 5.6.0 and 5.6.1 release tarballs contain an elaborate exploit that injects a backdoor into SSH. #Gentoo systems shouldn't be affected since our OpenSSH doesn't link to liblzma — apparently the exploit targets distributions that patch OpenSSH to link with libsystemd, which in turn may link to liblzma. However, it's not clear if the exploits doesn't do anything else, so we've masked the new versions.
lzip is not affected.
https://www.openwall.com/lists/oss-security/2024/03/29/4
2024-03-31 02:06:49
okay, it's pretty wild that with the #xz stuff there might never be a reliable network scanner for it (which seems like the most metal of exploits, but also might be just a limitation of over-the-network scans vs binary analysis)
e.g., if you don't have the secret key, it acts like normal
so there's no tell that it's a backdoor
unless there's some sort of bug in the logic
unless you somehow get the private key in a leak, in which case... try to log into all SSH daemons.
2024-03-29 23:43:04
Told my cat about the whole SSH xz thing but she just sneezed on my monitor and went back to sleep
2024-02-15 04:36:01
2024-04-17 00:50:01
Technical sysadmin-ish question. We've had our family mail hosted at a bullshit rinky-dink server since forever, we pay too much, and today we had a mail glitch because some bullshit automated IP address filter triggered.
So, what's the process for transferring a domain name, plus all the IMAP mail on those servers? We have ssh access to a server, even. I researched this once, I think something like "Dovecot" is part of the answer. Not sure if I should look at blueho…
2024-03-30 12:42:27
A backdoor in a popular Linux utility has been discovered, compromising encrypted SSH connections. https://reddit.com/r/cybersecurity/comments/1brdrgc/
2024-02-19 18:02:21
problem of using @… ssh lol:
Setting up tailscale (1.60.0) ...
Connection to pi5 closed by remote host.
Connection to pi5 closed.
2024-03-29 23:43:04
Told my cat about the whole SSH xz thing but she just sneezed on my monitor and went back to sleep
2024-04-15 09:53:02
Linux: oh no someone installed a very complex hidden backdoor on SSH please everyone panic
Windows: looks like we are installing a new service that leaks data on all servers without asking. Deal with it.
2024-02-09 21:53:42
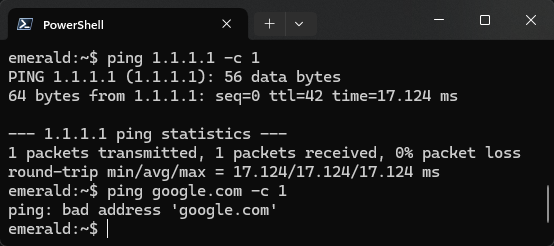
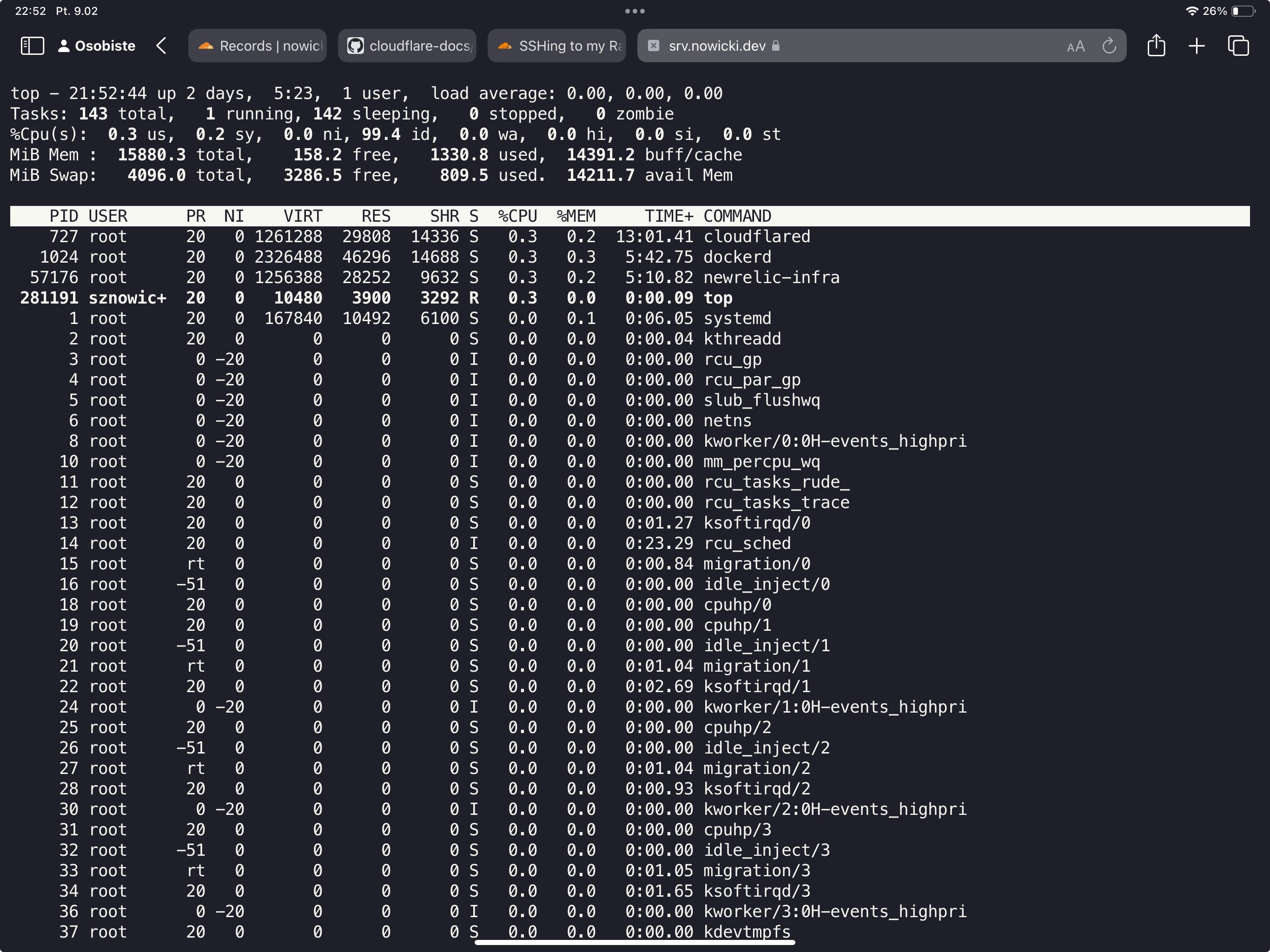
CloudFlare is simply amazing. I have now SSH terminal in a browser on https://srv.nowicki.dev with a proper authentication and everything.
All in less than 5 minutes.
2024-04-17 03:58:53
holy shit, i... solved bufferbloat (in one direction) in my userspace Python Linux network interface card driver in Glasgow?
i'm sending 200 Mbps of spam to Wanda's laptop right now (most of which doesn't fit into the 100M link) and pings never go above 25ms
also she gets acceptable realtime performance (ssh, etc)
I: g.applet.interface.ethernet_rgmii: usb->os pps= 16 Mbps= 0.03
I: g.applet.interface.ethernet_rgmii: os->usb pps=17862 Mbps=215.87
 @zimpenfish@social.rjp.is
@zimpenfish@social.rjp.is2024-03-15 09:35:08
Anyone got a good suggestion as to why pledge: filesystem during ssh login might be hanging for 90s? dmesg and sshd logs have nothing obvious. Nothing helpful in the internet searches either.
2024-04-12 21:19:21
The one thing I am dreading about Godot/iPad is setting up the CI on Xcode Cloud.
Those devices are powered by modded raspberry pis running MacOS.
I am thinking that one hack might be to use GitHub CI custom runners that SSH into my Studio to do the heavy lifting, and then use those binaries as the input to Xcode Cloud.
2024-04-02 05:35:24
«Die Feiertage. Die ganzen IT-Abteilungen feiern mit der Familie… Die ganzen IT-Abteilungen? Nein! Eine von unbeugsamen Open-Source-Enthusiasten bevölkerte Mailingliste hört nicht auf, den Eindringlingen Widerstand zu leisten.»
#xz #xzbackdoor #lzma #ssh
https://dnip.ch/2024/04/02/xz-open-source-ostern-welt-retten/
2024-03-29 17:54:21
oss-security - Backdoor in upstream xz/liblzma leading to ssh server compromise https://www.openwall.com/lists/oss-security/2024/03/29/4
2024-03-29 22:42:28
An upstream xz/liblzma backdoor leads to an SSH server compromise. https://reddit.com/r/cybersecurity/comments/1bqw8yc/
2024-03-13 02:54:45
2024-03-15 23:35:27
I installed #LibreElec on a pi4. During setup, it asked if I wanted to enable sshd (which, like, *of course* I do).
Then it told me the default login and password, and suggested that I change the password. Okay, sure, good idea. I tried a shared, memorable password I use for home appliance devices (NAT'd & only accessible via sudo, as I use ssh keys). "Password too weak&…
2024-03-29 22:42:28
An upstream xz/liblzma backdoor leads to an SSH server compromise. https://reddit.com/r/cybersecurity/comments/1bqw8yc/
2024-03-01 07:00:47
Electron conductance of a cavity-embedded topological 1D chain
Danh-Phuong Nguyen, Geva Arwas, Cristiano Ciuti
https://arxiv.org/abs/2402.19244 https://
2024-02-25 16:09:22
VNC through ssh tunnel http://localhost
2024-03-29 07:07:05
Dynamic Phase Enabled Topological Mode Steering in Composite Su-Schrieffer-Heeger Waveguide Arrays
Min Tang, Chi Pang, Christian N. Saggau, Haiyun Dong, Ching Hua Lee, Ronny Thomale, Sebastian Klembt, Ion Cosma Fulga, Jeroen Van Den Brink, Yana Vaynzof, Oliver G. Schmidt, Jiawei Wang, Libo Ma
https://arxiv.org/abs/2403.19427
 @zimpenfish@social.rjp.is
@zimpenfish@social.rjp.is2024-03-15 09:37:04
Switched to dropbear for now because bloody hell, waiting for 90s on every ssh/scp is painful.
2024-03-13 22:08:59
Alright, what's everyone's favorite (#selfhosted) blog software these days? Ideally something that doesn't require complicated setup (ie, Ghost is overkill, and I definitely don't need something backed by mysqld) and a million dependencies. I'd be fine with anything from uploading markdown text files over ssh, to editing with a web interface for new posts.
Also n…
2024-05-01 07:00:53
Topology in a Su--Schrieffer--Heeger plasmonic crystal
D. A. Miranda, Y. V. Bludov, N. Asger Mortensen, N. M. R. Peres
https://arxiv.org/abs/2404.19576 htt…
2024-03-25 07:01:39
Magnetic, charge, and bond order in the two-dimensional Su-Schrieffer-Heeger-Holstein model
Max Casebolt, Chunhan Feng, Richard T. Scalettar, Steven Johnston, G. G. Batrouni
https://arxiv.org/abs/2403.15386
2024-04-23 08:52:22
This https://arxiv.org/abs/2404.11084 has been replaced.
initial toot: https://mastoxiv.page/@arX…
2024-04-10 18:26:32
If you have a shoe string budget and can't afford a service like @… (and/or you're depending on fail2ban as a preventative control), this Dictionary Based Blocking looks to be very effective.
This research paper has tons of interesting tidbits. Worth the read! Or if you're going to #NSDI24, you can see a presentation by @…
#infosec #ssh #bruteforce #hacking #research
https://discuss.systems/@ricci/112247553557306560
2024-03-29 07:07:05
Dynamic Phase Enabled Topological Mode Steering in Composite Su-Schrieffer-Heeger Waveguide Arrays
Min Tang, Chi Pang, Christian N. Saggau, Haiyun Dong, Ching Hua Lee, Ronny Thomale, Sebastian Klembt, Ion Cosma Fulga, Jeroen Van Den Brink, Yana Vaynzof, Oliver G. Schmidt, Jiawei Wang, Libo Ma
https://arxiv.org/abs/2403.19427
2024-02-13 13:15:15
Topological Edge States in Reconfigurable Multi-stable Mechanical Metamaterials
Zhen Wang, Feiyang Sun, Xiaodong Xu, Xin Li, Chuanqing Chen, Minghui Lu
https://arxiv.org/abs/2402.07707
2024-04-23 08:52:22
This https://arxiv.org/abs/2404.11084 has been replaced.
initial toot: https://mastoxiv.page/@arX…
2024-04-15 06:47:58
Navigating Quantum Security Risks in Networked Environments: A Comprehensive Study of Quantum-Safe Network Protocols
Yaser Baseri, Vikas Chouhan, Abdelhakim Hafid
https://arxiv.org/abs/2404.08232
2024-04-10 18:26:32
If you have a shoe string budget and can't afford a service like @… (and/or you're depending on fail2ban as a preventative control), this Dictionary Based Blocking looks to be very effective.
This research paper has tons of interesting tidbits. Worth the read! Or if you're going to #NSDI24, you can see a presentation by @…
#infosec #ssh #bruteforce #hacking #research
https://discuss.systems/@ricci/112247553557306560
2024-04-24 07:21:33
Towards electrical domain-wall control in polyacetylene-based electronic nanodevices
Leandro M. Arancibia, Andr\'es I. Bertoni, Cristi\'an G. S\'anchez, Alejandro M. Lobos
https://arxiv.org/abs/2404.15257
2024-04-15 07:22:37
Quantum geometric tensor and the topological characterization of the extended Su-Schrieffer-Heeger model
Xiang-Long Zeng, Wen-Xi Lai, Yi-Wen Wei, Yu-Quan Ma
https://arxiv.org/abs/2404.08222
2024-02-13 13:15:15
Topological Edge States in Reconfigurable Multi-stable Mechanical Metamaterials
Zhen Wang, Feiyang Sun, Xiaodong Xu, Xin Li, Chuanqing Chen, Minghui Lu
https://arxiv.org/abs/2402.07707
2024-03-19 07:07:11
Scattering Singularity in Topological Dielectric Photonic Crystals
Langlang Xiong, Xunya Jiang, Guangwei Hu
https://arxiv.org/abs/2403.11613 https://
2024-04-19 08:40:21
This https://arxiv.org/abs/2404.11084 has been replaced.
initial toot: https://mastoxiv.page/@arX…
2024-02-13 13:13:08
Weakly interacting one-dimensional topological insulators: a bosonization approach
Polina Matveeva, Dmitri Gutman, Sam T. Carr
https://arxiv.org/abs/2402.07239
2024-04-18 07:31:38
Observation of Young's double-slit phenomenon in anti-PT-symmetric electrical circuits
Xiumei Wang, Keyu Pan, Xizhou Shen, Xingping Zhou
https://arxiv.org/abs/2404.11084
2024-03-11 07:00:33
Extreme anti-ohmic conductance enhancement in neutral diradical acene-like molecular junctions
Brent Lawson, Efrain Vidal, Michael M. Haley, Maria Kamenetska
https://arxiv.org/abs/2403.04906